Threat Talks
Recent Episodes
Russia Cutting Cables? Who’s Protecting It?
Find Threat Talks onRussia Cutting Cables? Who’s Protecting It? The headlines say Russia’s shadow fleet is cutting cables. The experts say most faults come from clumsy ship anchors. Ninety-nine percent of global internet traffic runs across the ocean floor, and the...
Hero Culture and a $1 Million Mistake
Saying no doesn’t stop the risk, it moves it out of sight. Sina Yazdanmehr and Lieuwe Jan Koning on hero culture, the Department of No, and the $1M risk lesson.
When Compliance Replaces Security
Find Threat Talks onWhen Compliance Replaces Security Compliance is not security. Security culture is company culture. If your employees do not trust their managers, no policy you write will save you. Sina Yazdanmehr, Founder and Managing Director of Aplite GmbH,...
The Agent Problem
Find Threat Talks onThe Lethal Triangle: Why Your Agent Is a Breach Vector Agentic AI has put autonomous software inside your systems, with your permissions, against the data you’re paid to protect, and most organizations don’t yet have a security model for it. In...
Your Sales Team is now a Developer
Your team is already using AI coding agents – whether you know it or not. Find out what that means for your security, and what to do about it.
The Hidden Risk of Your Infrastructure
Find Threat Talks onThe Hidden Risk of Your Infrastructure Nation state actors have been targeting critical infrastructure for years, and most organizations are not as prepared as they think. The risk is not just about who is trying to get in. It is about what is...
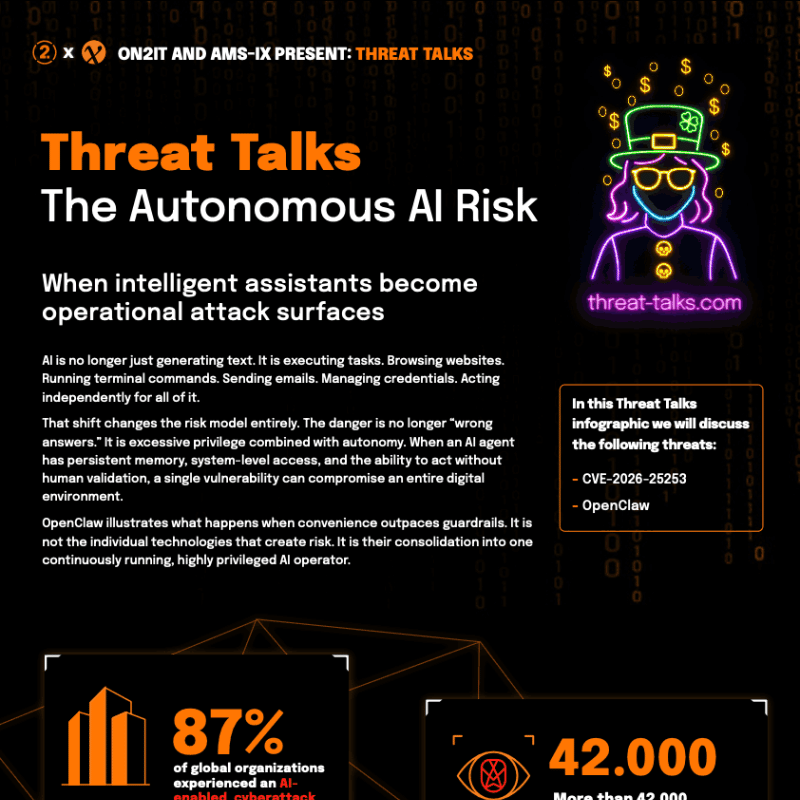
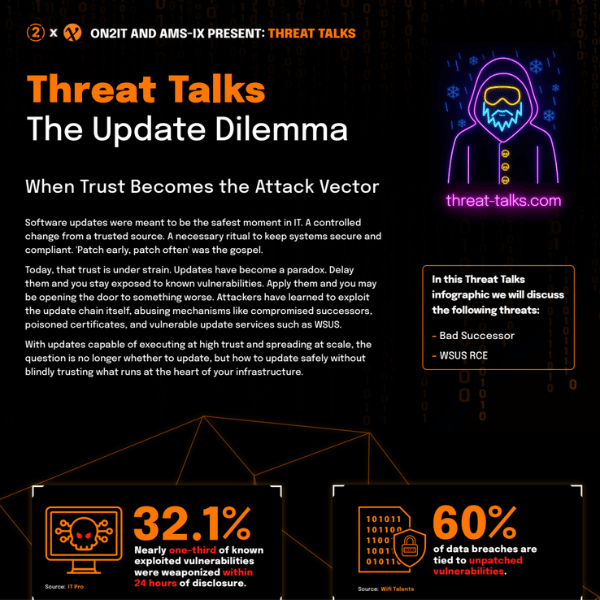
Cybersecurity Infographics
JOIN THE CYBERSECURITY CONVERSATION
Subscribe to Threat Talks for in-depth explorations of recent cybersecurity threats and trends, with exclusive insights and expert perspectives.